After analyzing leaked documents, Check Point Research (CPR) gives new details on the inside-operations of Conti, the notorious Russian ransomware group. Conti is structured like a high-technology company, with clear management, finance and HR functions. Conti recruits not only from underground, but legitimate sources, borrowing CV pools without permission. Some employees at Conti have no clue that they are part of a cybercriminal operation. CPR has also learned that Conti has future plans for a crypto exchange and a darknet social network.
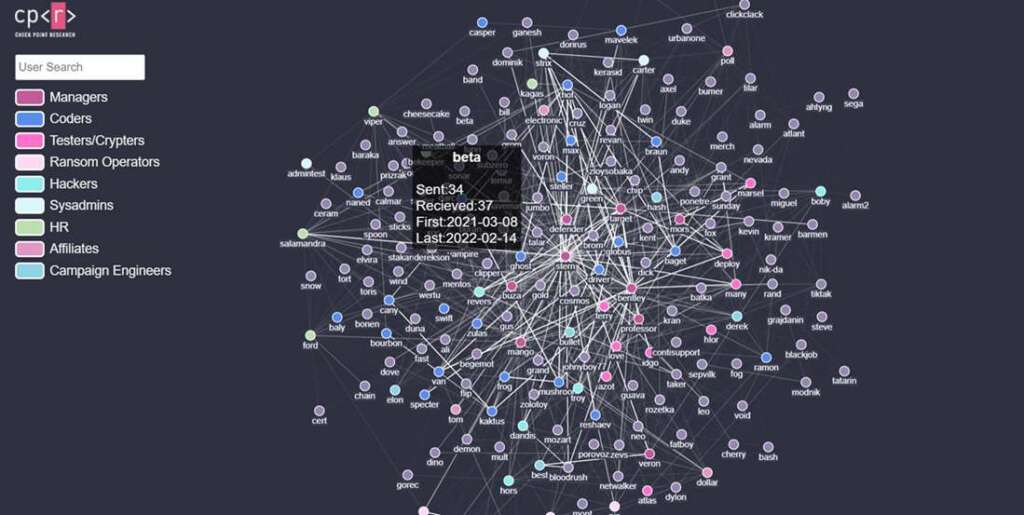
- CPR graphs organizational structure of Conti, highlighting key groups and people, named Stern, Bentley, Mango, Buza and more.
- Conti group has several physical offices, including in Russia
- Conti’s HR team offers monthly bonuses, fines, employee of the month and performance reviews
Check Point Research (CPR) has gained new details into the inside-operations of Conti ransomware group. Conti is a ransomware-as-a-service (RaaS) group, which allows affiliates to rent access to its infrastructure to launch attacks. Industry experts have said Conti is based in Russia and may have ties to Russian intelligence. Conti has been blamed for ransomware attacks targeting dozens of businesses, including clothing giant Fat Face and Shutterfly, as well as critical infrastructure, like the Irish healthcare service and other first-responders networks.
On February 27 of this year, a cache of chat logs belonging to the Conti were leaked online at the hands of an alleged insider, who claimed to have objected to the group’s support for the Russian invasion of Ukraine. CPR analyzed the leaked files, learning that the ransomware groups operates like a large technology company. Conti has an HR department, a hiring process, offline office premises, salaries and bonus payments.
Details of Conti’s Inside-Operations
1. Conti operates like a technology company
- Hierarchical and defined structure
- Team leaders who report to upper management
- Main groups observed: HR, coders, testers, crypters, sysadmins, reverse engineers, offensive team, OSINT Specialists and Negotiation Staff
- CPR identified the main people involved with their names: Stern (big boss), Bentley (technical lead), Mango (manager of general questions), Buza (technical manager), Target (manager responsible for coders and their products), Veron aka Mors (focal point of the group’s operations with Emotet).
- Work in a physical office in Russia
- The Conti group holds several physical offices. These are curated by “Target”, Stern’s partner and effective head of office operations, who is also responsible for the wage fund, office technical equipment, the Conti hiring process and personnel training. During 2020, offline offices were mainly used by testers, offensive teams and negotiators; Target mentions 2 offices dedicated to operators who are speaking directly with victim representatives.
- In August 2020, an additional office was opened for sysadmins and programmers, under the purview of “Professor, who is responsible for the whole technical process of securing a victim infection.
- Compensation: monthly bonuses, fines, employee of the month, performance reviews
- Members of Conti’s negotiating team (including OSINT specialists) are paid by commissions, calculated as a percentage of the paid ransom amount that ranges from 0.5% to 1%. Coders and some of the managers are paid a salary in bitcoin, transferred once or twice a month.
- Conti employees are not protected by their local labor boards, and so have to endure some practices that typical tech employees are exempt from, such as being fined for underperforming.
- While fines are mostly used as an established tool in the coder department, they are sporadically employed on manager whims in other departments — for example, in IT and DevOps, where one person responsible for depositing money was fined $100 for a missed payment:
2. Talent is recruited from both legitimate and underground sources
-
- The main resource typically used by Conti HR for hiring is Russian-speaking headhunting services such as headhunter.ru. They’ve also used other sites such as superjobs.ru, but reportedly with less success. Conti OPSec forbids leaving traces of developer job openings on such websites, a regulation stringently enforced by one of the higher-ups, “Stern”
- So for hiring developers, Conti bypasses the headhunter.ru job system, instead directly accessing the CV pool and contacting candidates by email. You might wonder “why does headhunter.ru offer such a service?”, and the answer is, they don’t. Conti simply “borrowed” the CV pool without permission, which seems to be standard practice in the cybercrime world
3. Some Conti employees don’t know they are even part of a cybercriminal operation
-
- In one online job interview, a manager tells a potential hire for the coding team: “everything is anonymous here, the main direction of the company is software for pentesters”.
- In another example, a group member known by the moniker “Zulas”, most likely the person who developed Trickbot’s backend in the Erlang programming language. Zulas is passionate about Erlang, eager to show examples of his other work, and even mentions his real name. When his manager mentions that his “trick” (Trickbot) project was seen by “half of the world”, Zulas does not understand the reference, calls the system “lero” and reveals that he has no idea what his software is doing and why the team goes to such lengths to protect member identities. His interlocutor tells him that he is working on a backend for an ad analytics system.
4. Conti is actively discussing future plans: crypto exchange and a darknet social network
-
- One of the ideas discussed was creating a crypto exchange in the group’s own ecosystem
- Another project is the “darknet social network” (also: “VK for darknet” or “Carbon Black for hackers”), a project inspired by Stern and carried out by Mango, planned to be developed as a commercial project. In July 2021 Conti was already in contact with a designer, who produced a few mockups.
Lotem Finkelsteen, Head of Threat Intelligence and Research, at Check Point Research:
“For the first time, we have a glass door to a group that has been known to be the face of ransomware. Conti acts like a high-tech company. We see hundreds of employees in a hierarchy of managers. We see an HR function, with people responsible for different departments. Alarmingly, we have evidence that not all the employees are fully aware that they are part of a cybercrime group. In other words, Conti has able to recruit professionals from legitimate sources. These employees think they are working for an ad company, when in fact they are working for a notorious ransomware group. Some of these employees find out the truth and they decide to stay, revealing that the Conti management team has developed a process for retaining employees. It’s clear to us that Conti has developed an internal culture to develop profits, as well as fining employees for undesirable behavior. We also see that Conti has offices in Russia. Our publication presents findings of the inner-working and culture of Conti.”
Appendix: Graph of Conti’s Organizational Structure
Link is here: https://research.checkpoint.com/wp-content/uploads/2022/03/map_index_v2.html